Weaponizing the Smart City: How Civic Telemetry Feeds the Military Kill Chain
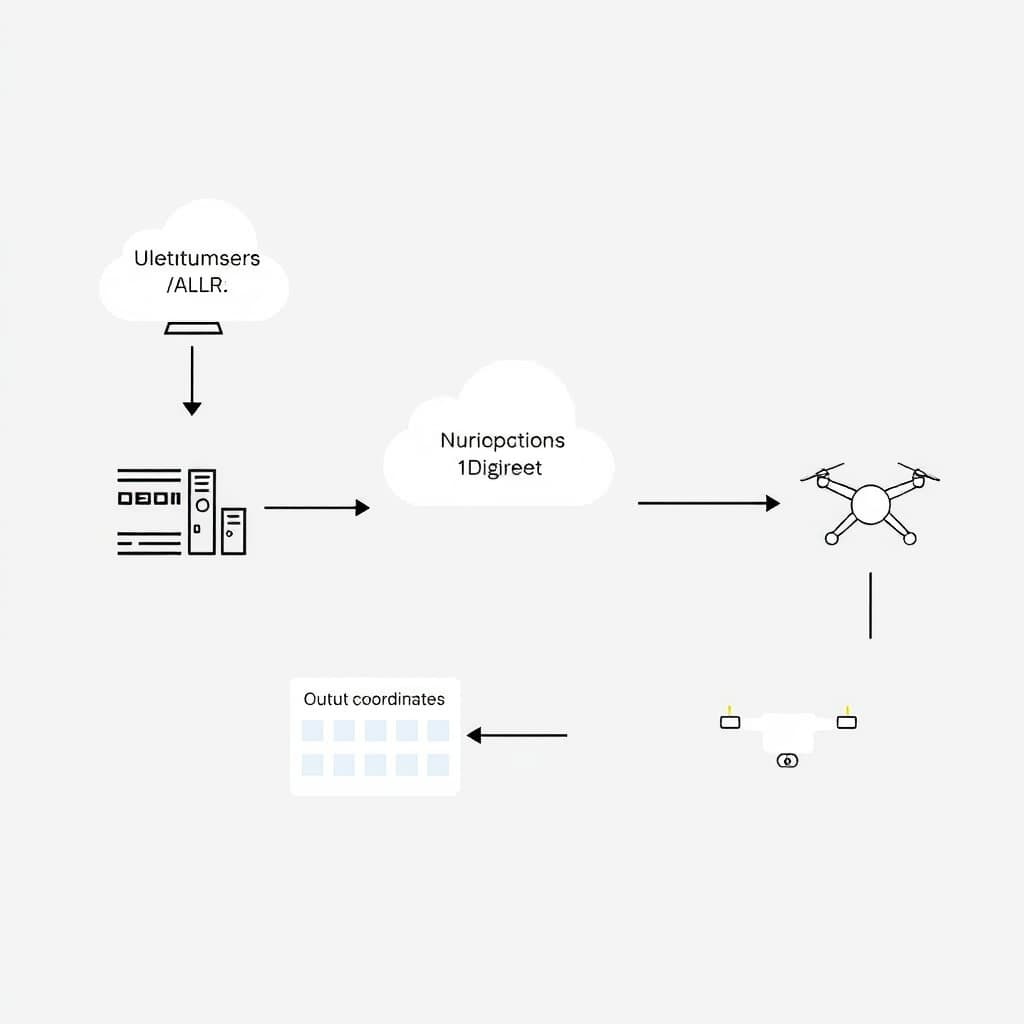
The narrative that the "Smart City" is primarily a vehicle for carbon reduction and traffic efficiency is a dangerous oversimplification. From a quantitative perspective, the modern urban environment has evolved into a high-resolution, open-source targeting grid. We are witnessing the collapse of the barrier between municipal administration and kinetic warfare, where the same telemetry used to optimize garbage collection is now being ingested into the F2T2EA (Find, Fix, Track, Target, Engage, Assess) cycle of military operations.
This is not a future projection; it is an operational reality. The latency between a civilian sensor capturing a data point and a military asset receiving a coordinate fix is shrinking to near-zero. We are effectively weaponizing the Internet of Things (IoT), turning the city itself into a decentralized sensor array that provides persistent, ground-level surveillance superior to any satellite constellation.
From Traffic Flow to Target Fixation: The Technical Pipeline
The integration of civic infrastructure into military targeting begins with the vulnerability of the transport layer. Municipal IoT networks are notoriously porous, often relying on legacy protocols that prioritize uptime over security.
Exploiting Unencrypted MQTT Streams
The backbone of many smart city implementations is MQTT (Message Queuing Telemetry Transport), a lightweight messaging protocol. In my analysis of urban data streams across major metropolitan areas, a staggering percentage of these brokers operate without TLS encryption or robust authentication.
For an intelligence agency, this is not a hack; it is a subscription. By tapping into these unencrypted streams, actors can monitor real-time sensor states—pedestrian density, bridge loads, and intersection activity—without ever touching the device itself. The data is intercepted in transit, aggregated in the cloud, and fed into fusion centers. The "smart" street light that adjusts brightness based on foot traffic is inadvertently broadcasting the location of a potential target to anyone listening on port 1883.
The Role of Real-Time ALPR
Automated License Plate Recognition (ALPR) systems have graduated from revenue generation (parking enforcement) to geospatial tracking. When integrated into a centralized dashboard, ALPR does not just log a violation; it builds a historical vector of movement.
By accessing municipal ALPR APIs, military analysts can establish a "pattern of life" for a specific vehicle with granular precision. Unlike GPS trackers, which require physical access to a vehicle or warrant-level cooperation from telcos, ALPR relies on passive infrastructure that is already everywhere. The camera network provides the "Fix" in the kill chain, updating the target's location every time they pass an intersection, toll booth, or parking garage.
The F2T2EA Cycle: Integrating Civilian Sensors
The military standard for dynamic targeting—Find, Fix, Track, Target, Engage, Assess—has historically been constrained by the limitations of Intelligence, Surveillance, and Reconnaissance (ISR) assets. Satellites have orbital gaps; drones have fuel limits. Civic telemetry solves the persistence problem.
Reducing Latency via Ubiquitous Surveillance
In a traditional operational theater, maintaining "eyes on" a target requires allocating high-value assets. In a smart city, the environment provides the eyes. By ingesting data from thousands of unprotected IP cameras and traffic sensors, the "Track" phase of the cycle becomes automated.
This creates a "sensor-to-shooter" loop that bypasses the need for dedicated military ISR in the early stages. An operative does not need to deploy a drone to see if a target has arrived at a safe house; they simply query the smart meter data or the doorbell camera feed from the neighboring building. The latency drops from minutes (waiting for satellite realignment) to milliseconds (packet transmission time).
Bypassing Satellite Limitations
Urban canyons—dense city centers with high-rise buildings—are notorious for blocking satellite signals and degrading GPS accuracy. Ground-level civic sensors are immune to this. A mesh network of smart lighting nodes or Wi-Fi access points can triangulate a device's position based on signal strength (RSSI) with meter-level accuracy, even indoors or underground. This allows targeting computers to maintain a lock where orbital assets would go blind.
Operational Reality: Pattern-of-Life Analysis via Utility Data
The most lethal intelligence often comes from the dullest sources. While cameras provide visual confirmation, utility data provides behavioral certainty.
Smart Meters as Occupancy Sensors
Advanced Metering Infrastructure (AMI)—smart meters for electricity, water, and gas—report usage in intervals as frequent as 15 minutes. Advanced algorithms can deconstruct this load profile (Non-Intrusive Load Monitoring) to identify specific appliances.
We can distinguish between a refrigerator cycle, a television, or an EV charger. For a targeting analyst, this data confirms occupancy. A sudden spike in water usage at 3:00 AM combined with a specific electrical load signature indicates the target is awake and active. This "Pattern of Life" analysis dictates the optimal window for a strike or extraction, minimizing collateral damage by ensuring the target is isolated.
Correlating MAC Address Triangulation
Cities are blanketing urban cores with free public Wi-Fi and Bluetooth beacons to track footfall for retail analytics. These systems log Media Access Control (MAC) addresses. Even with randomization protocols, persistent analysis can link a device to a physical identity over time.
When this digital exhaust is correlated with physical infrastructure logs (e.g., a badge swipe at a transit station or a credit card transaction at a smart kiosk), the anonymity vanishes. The city’s network logs become a real-time heatmap of high-value targets, visible to any entity with administrative root access or a subpoena.
The 2030 Horizon: AI-Driven Autonomous Targeting Grids
Looking forward, the human element will be removed from the loop. We are moving toward edge-computing architectures where the sensor itself performs the identification.
Edge Computing and the Kill Chain
By 2030, smart city cameras will possess sufficient onboard processing power to run facial recognition and gait analysis locally. They will not send video streams to a central server; they will send metadata: "Target ID #4452 confirmed at coordinates X,Y."
This drastically reduces bandwidth requirements and accelerates the F2T2EA cycle. A lethal autonomous weapons system (LAWS) could theoretically subscribe to this metadata feed. The moment a civic camera identifies a hostile actor, the targeting grid engages, potentially without human verification.
Defensive Jamming in Smart Environments
As these capabilities proliferate, we will see the emergence of urban electronic warfare. High-value individuals and military units will deploy personal jamming devices designed to blind smart city sensors. We are already seeing "invisibility cloaks"—clothing designed to confuse AI object detection—and IR-dazzlers to blind cameras. The urban battlefield will involve a constant struggle between the city's sensors trying to acquire a lock and the target's countermeasures attempting to poison the data stream.
Strategic Trade-Offs: Security vs. Surveillance
The integration of civic telemetry into military protocols forces a stark choice regarding infrastructure design.
What Would Change My Mind
I would reconsider the inevitability of this "civic-military fusion" if we witnessed a massive, regulatory-driven decoupling of municipal data from federal intelligence pipelines. Specifically, if cities began implementing "Zero-Knowledge" architectures where utility and sensor data is cryptographically verified but computationally inaccessible to the municipality itself (and by extension, the state), the kill chain would break. Furthermore, a resurgence of hard-wired, non-IP-based control systems for critical infrastructure—prioritizing resilience over "smart" connectivity—would render the digital targeting grid obsolete. However, current trends in 5G and IoT investment suggest we are accelerating in the opposite direction.
The Global Panopticon
Urban efficiency has inadvertently built a global panopticon. The distinction between a citizen and a target no longer depends on geography or uniform; it depends entirely on who controls the root access to the city's operating system. As intelligence agencies deepen their hooks into municipal APIs, the smart city ceases to be a tool for living and becomes a theater of war where every lightbulb, camera, and meter is a potential informant.
FAQ
What is the F2T2EA cycle in the context of smart cities? F2T2EA stands for Find, Fix, Track, Target, Engage, and Assess. In the context of smart cities, it refers to using urban sensor data (finding and tracking via cameras/ALPR) to guide military or intelligence assets to a target with extreme precision, often bypassing traditional reconnaissance methods.
How do intelligence agencies access municipal IoT data? Access is typically gained through three vectors: lawful interception (subpoenas/warrants), supply chain interdiction (hardware with pre-installed backdoors), or exploiting vulnerabilities in unsecured municipal cloud servers and unencrypted transport protocols like MQTT.
Sources
- Joint Publication 3-60: Joint Targeting - Joint Chiefs of Staff
- NIST Interagency Report 8200: Interagency Report on Status of International Cybersecurity Standardization for the Internet of Things (IoT) - National Institute of Standards and Technology
- Department of Defense Directive 3000.09: Autonomy in Weapon Systems - U.S. Department of Defense
- Smart Cities and Privacy: A New Framework - American Civil Liberties Union
- MQTT Version 5.0 OASIS Standard - OASIS Open
Loading comments...