

Sovereign Blackout Liquidity: How Nation-States Move Capital When the Grid Goes Dark
Chief Information Security Officers, central bank regulators, and sovereign risk analysts face an escalating blind spot: calculating capital flight risk when telecommunications infrastructure goes completely dark. Operating from Seoul, where the proximity to the Democratic People's Republic of Korea (DPRK) and its cyber-warfare operations provides a stark vantage point, I observe this threat model evolving daily. Traditional frameworks assume that severing internet access halts unauthorized financial outflows. That assumption is fatally flawed. I will deconstruct the exact technical mechanisms nation-states and sanctioned entities deploy to execute massive cryptocurrency transfers during total grid failures, evaluating the physical layer workarounds, on-chain forensics, and the regulatory countermeasures defining the 2026 geopolitical battlefield.
When physical infrastructure crumbles under conflict, state actors do not lose access to their capital. By leveraging tools originally designed for financial inclusion—such as satellite blockchain broadcasts and localized mesh networks—sanctioned entities bypass legacy choke points. The Financial Action Task Force (FATF) recently highlighted that the mass adoption of virtual assets amplifies illicit finance risks, especially when oversight of offshore providers remains fractured.
Bypassing the Grid: The Mechanics of Offline Transaction Broadcasting
To understand how capital moves without internet service providers, we must separate transaction generation from transaction broadcasting. A dark grid blinds domestic surveillance, but it does not destroy the underlying cryptographic wealth.
Mesh Networks and Low-Earth Orbit Satellites
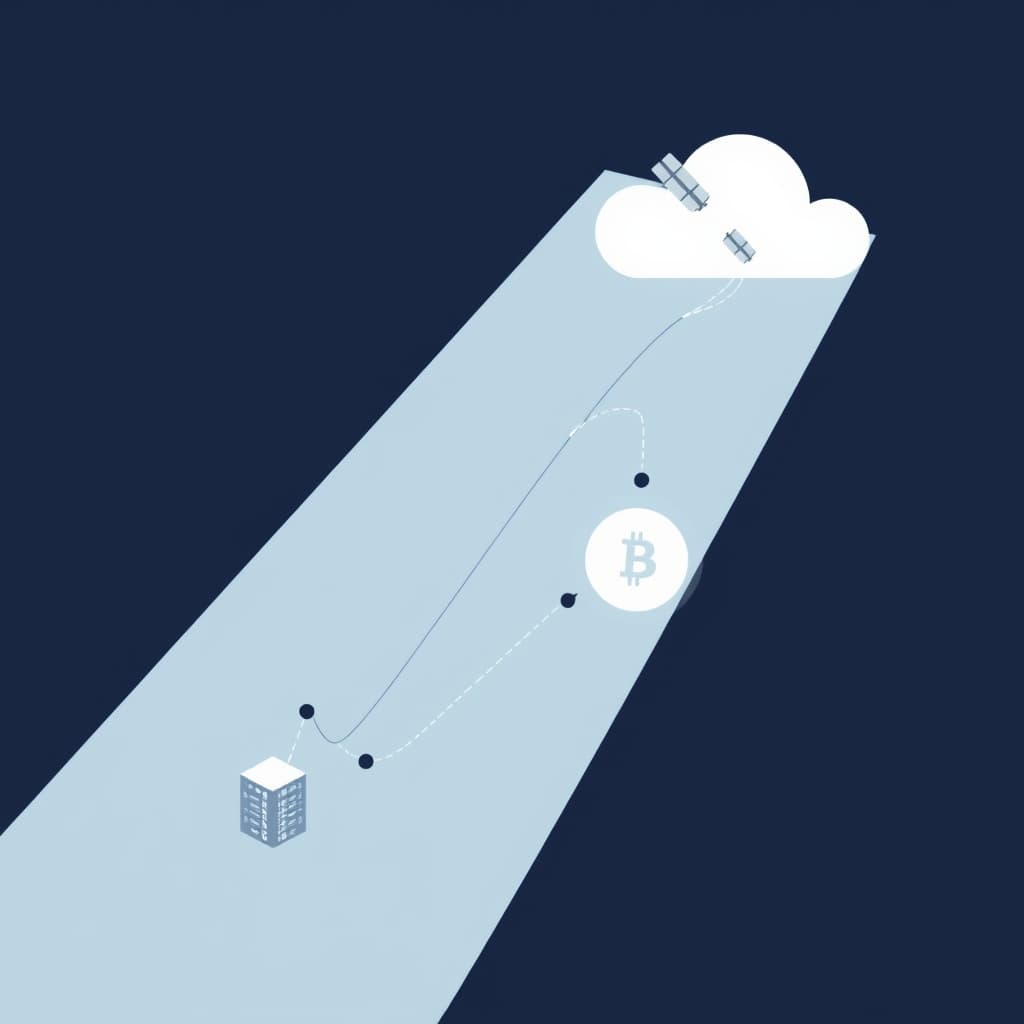
State actors utilize hybrid physical-layer networks to maintain continuous synchronization with global ledgers. The Blockstream Satellite network, for example, leases commercial geosynchronous satellites—such as Telstar and Galaxy—to beam the Bitcoin blockchain down to Earth 24/7. Anyone with a basic TV satellite dish and a USB receiver can sync a full node passively, leaving zero digital footprint.
To send funds out of a blackout zone, entities deploy localized mesh networks utilizing protocols like LoRaWAN, or they execute shortwave radio bursts. These low-bandwidth physical layers relay signed cryptographic hex-data across borders, bouncing from node to node until the transaction hits an internet-connected terminal outside the blackout radius.
Asymmetric Cryptography in Air-Gapped Environments
The actual signing of these multi-million dollar transfers happens in subterranean or heavily shielded air-gapped environments. Using Partially Signed Bitcoin Transactions (PSBTs), a state-sponsored wealth manager constructs a transaction on an offline machine. The manager signs it using cold-stored private keys and transfers the cryptographic proof via QR code or encrypted micro-SD to a transmission relay. The private keys never touch an internet-connected device, neutralizing traditional network intrusion tactics.
Geopolitical Resilience Through Decentralized Ledgers
The migration from centralized banking to decentralized infrastructure is not ideologically driven for state actors; it is a pragmatic necessity for regime survival.
Why State Actors Abandon Legacy Banking During Kinetic Conflicts
The DPRK provides the definitive case study in decoupling sovereign wealth from legacy banking. When isolated from the SWIFT network, the DPRK’s Lazarus Group pivoted entirely to decentralized ledgers. Recent 2026 blockchain analytics confirm that state-sponsored IT worker networks and cyber syndicates generated nearly $800 million in 2024 alone to fund weapons of mass destruction programs. They execute cross-chain bridge hops and utilize offshore Virtual Asset Service Providers (VASPs) located in Southeast Asia to liquidate assets. Kinetic isolation does not equal financial isolation when liquidity is mathematically guaranteed by a distributed network.
Mitigating Financial Seizure via Distributed Nodes
Legacy banking relies on centralized databases where a single administrative edit can freeze billions in fiat currency. Decentralized nodes require network consensus, neutralizing unilateral seizure commands. When the U.S. Office of Foreign Assets Control (OFAC) sanctioned cryptocurrency mixers like Blender.io and Sinbad, they targeted the front-end service interfaces. Yet, the underlying smart contracts remain immutable.
The legal framework for seizing these assets is highly volatile. A landmark November 2024 Fifth Circuit Court of Appeals ruling determined that autonomous smart contracts—specifically those powering the Tornado Cash protocol—do not constitute actionable "property" under the International Emergency Economic Powers Act (IEEPA). This ruling severely complicates the Treasury's ability to act against decentralized, open-source privacy technologies, forcing regulators to rethink their containment strategies.
Tracking the Untrackable: On-Chain Signatures of Sovereign Wealth Flight
While the broadcast physical layer may be obscured by a blackout, the eventual settlement on a public ledger leaves an indelible forensic trail.
Volume Anomalies Preceding Infrastructure Sabotage
Forensic analysts monitor mempool data for specific anomalies that reliably precede physical grid failures. Days before a targeted telecommunications blackout, on-chain liquidity often spikes. Sovereign wealth managers consolidate Unspent Transaction Outputs (UTXOs) into highly liquid stablecoins, preparing for the offline physical transport of seed phrases or low-bandwidth radio transmission. A sudden consolidation of dormant state-linked wallets is a high-confidence indicator of impending infrastructure disruption.
Heuristics of State-Sponsored Wallet Clusters
Identifying state-sponsored activity requires moving beyond basic address blacklists. The FATF's recent targeted updates note that stablecoins now dominate illicit on-chain activity. Analysts look for "chain-hopping" patterns—rapidly converting stolen Ethereum to Tron-based USDT, then funneling it through non-compliant offshore VASPs. The designation of addresses across multiple blockchain networks reflects an increasingly multi-chain approach to moving sovereign funds.
The Global Regulatory Response to Dark-Grid Capital Movements
Because regulators cannot subpoena a satellite or arrest a mesh network protocol, enforcement agencies are shifting their targeting parameters to the human and hardware layers.
OFAC Target Adjustments for Non-Standard Network Relays
Enforcement is migrating from the software layer to the physical supply chain. OFAC now designates the human facilitators, over-the-counter (OTC) brokers, and the hardware logistics networks enabling these dark-grid transfers. Designating specific Ethereum and Tron addresses associated with state-controlled IT companies—such as the Amnokgang Technology Development Company—demonstrates a strategic pivot. Authorities are no longer just targeting financial institutions; they are targeting the cryptographic identities of state apparatuses.
The Future of Infrastructure-Level Sanctions Enforcement
The FATF’s late-2025 Asset Recovery Guidance mandates that jurisdictions treat virtual assets as a distinct asset class requiring specialized seizure protocols. Law enforcement personnel are now trained to identify hardware wallets, seed phrases etched into physical metal, and mesh radio equipment during physical raids. The regulatory battlefield has permanently expanded from bank compliance departments to the physical hardware layer operating at the tactical edge.
The Next Frontier of Financial Warfare
Nation-states have successfully decoupled financial survival from physical telecommunications infrastructure. Monitor the development of sovereign-backed mining pools and proprietary satellite relays as the next phase in geopolitical financial warfare. The assumption that a dark grid equals a frozen treasury is entirely obsolete.
FAQ
How can a transaction be broadcast without standard internet service providers? Entities utilize satellite uplinks, localized mesh networks, and even shortwave radio bursts to transmit signed transaction data to blockchain nodes located outside the blackout zone.
What volume of capital is routed through these blackout channels? On-chain analytics reveal sudden multi-million dollar liquidity spikes from state-controlled wallets that perfectly correlate with localized telecom infrastructure outages.
Sources
- U.S. Department of the Treasury: OFAC Sanctions Individuals Facilitating DPRK IT Worker Fraud
- Financial Action Task Force (FATF): Virtual Assets
- Blockstream Satellite GitHub Repository
- Chainalysis: OFAC Targets North Korean IT Worker Networks Using Cryptocurrency
- Hogan Lovells: U.S. Appeals Court limits OFAC’s sanctions authority in cryptocurrency mixer case
Loading comments...
Related
View all →

Bridging Wall Street and Web3: The Rise of Tokenized Equity Interoperability Rails

The Balance Sheet Pivot: How Prudential Regimes Are Forcing Crypto into Tier 1 Banks


