
Quantum-Resistant Sidechain Fortification: Surviving the Q-Day Threat
Quantum-Resistant Sidechain Fortification: Surviving the Q-Day Threat
On March 3, 2026, Blockstream Research broadcast the first post-quantum signed transactions on a production Bitcoin sidechain, locking real user assets on the Liquid Network behind hash-based cryptography. This deployment bypasses base-layer consensus bottlenecks by utilizing the Simplicity smart contract language to enforce custom spending conditions. Evaluating cryptographic infrastructure for over 15 years requires distinguishing between theoretical vulnerabilities and actionable engineering solutions. Quantum computers are accelerating toward a threshold capable of breaking legacy cryptographic algorithms, putting foundational blockchain security at existential risk. We examine the proactive deployment of post-quantum signatures, specifically focusing on the SHRINCS implementation on Bitcoin's Liquid network, to reveal how developers are shielding critical infrastructure today.
The Cryptographic Ticking Clock and Shor's Algorithm
Vulnerabilities in Elliptic Curve Digital Signature Algorithm (ECDSA)
The security of nearly all modern decentralized networks rests on the Elliptic Curve Digital Signature Algorithm (ECDSA), specifically the secp256k1 curve. ECDSA relies on the discrete logarithm problem—a mathematical trapdoor that is practically impossible for classical computers to reverse but highly susceptible to Shor's algorithm. When a quantum computer reaches sufficient scale, it can calculate the private key from a public key in polynomial time. The immediate operational risk surfaces whenever a public key is exposed to the ledger. While best practices dictate using addresses only once, millions of legacy UTXOs—including the earliest mined blocks—have their public keys permanently visible, creating a massive, static attack surface.
Defining the Q-Day Horizon for Decentralized Networks
Predicting "Q-Day"—the exact moment a quantum computer breaks 256-bit elliptic curve cryptography—remains an exercise in probability, but the timeline is compressing. Recent assessments from quantum research divisions indicate that breaking ECDLP-256 could theoretically require fewer than 1,200 logical qubits, a sharp reduction from earlier estimates. Fault-tolerant hardware of this scale does not exist in 2026, yet the threat model for financial infrastructure demands a decade of lead time for safe migration. Malicious actors are currently incentivized to record encrypted traffic and identify high-value blockchain addresses in preparation for the moment quantum hardware comes online.
Integrating SHRINCS on the Liquid Network
Transitioning from Legacy Multi-Sig to Post-Quantum Standards
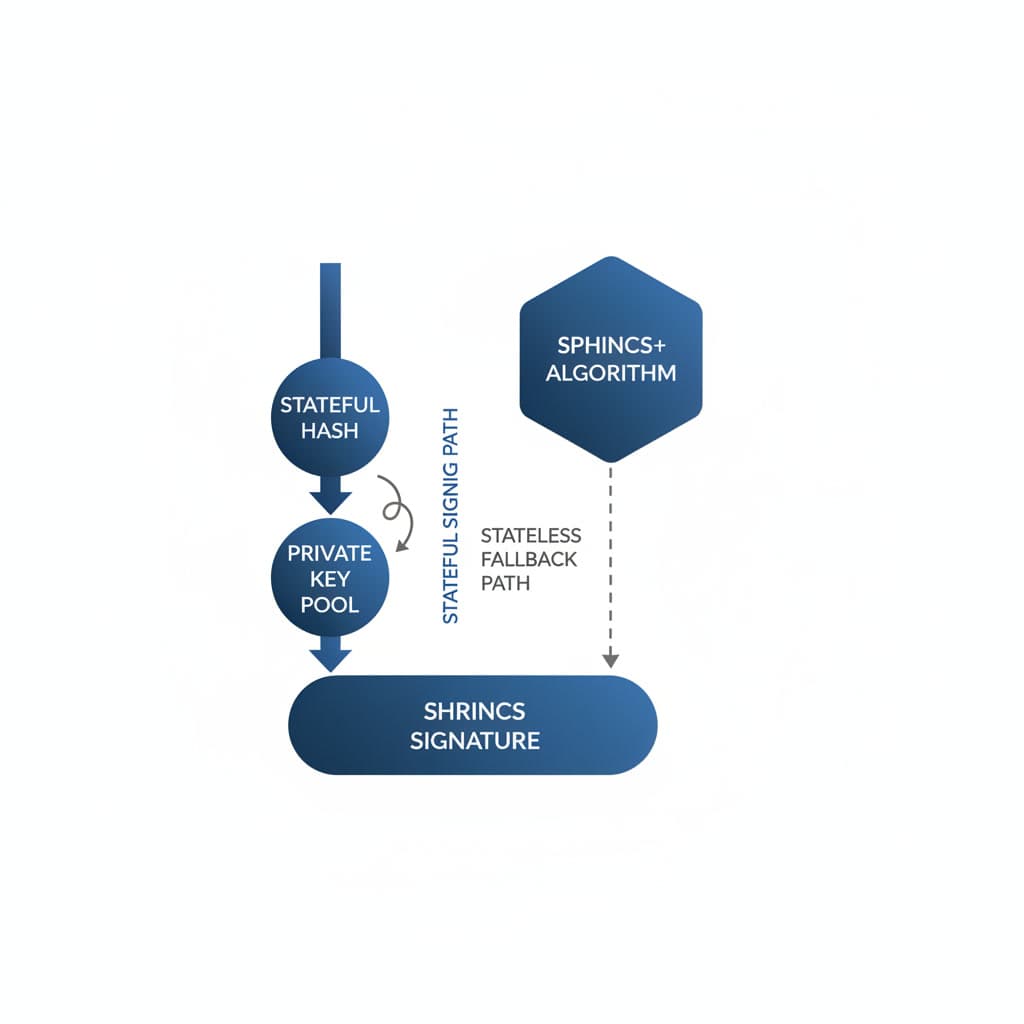
Upgrading a live financial network requires balancing security with strict computational constraints. Blockstream's deployment of SHRINCS (a hybrid hash-based signature scheme) on the Liquid sidechain serves as a live-fire case study in this transition. SHRINCS combines a stateful unbalanced XMSS tree for routine, highly efficient signing with a stateless fallback (a variant of SPHINCS+) to prevent catastrophic fund loss if the signing device's state is corrupted or lost. Users opt into this protection by locking their Liquid assets—such as L-BTC or tokenized securities—into a Simplicity smart contract. The contract strictly requires a valid post-quantum signature for any future spend, effectively walling off the assets from quantum interception without altering Liquid's underlying consensus rules.
Minimizing Blockchain Bloat with Optimized Signature Sizes
Blockchain architecture inherently penalizes large data payloads. Standard post-quantum algorithms approved by NIST, such as ML-DSA or SLH-DSA, produce signatures ranging from 3 KB to over 7.8 KB. Broadcasting signatures of this magnitude for every transaction would congest block space and render fees economically unviable.
The SHRINCS implementation solves this geometric scaling problem through its stateful path. By securely tracking the number of signatures generated, the primary device can produce a cryptographic proof of roughly 324 bytes. Only in emergency recovery scenarios does the system default to the larger stateless signature.
Spillover Effects for Bitcoin-Adjacent Infrastructure
Enhancing Cross-Chain Peg Mechanisms against Quantum Interception
Sidechains rely on two-way peg mechanisms to transfer value from the base layer. These bridges are typically secured by a federated multi-signature wallet. If the federation's cryptographic threshold relies entirely on ECDSA, the entire reserve backing the sidechain's assets becomes a single point of failure. A quantum adversary capable of forging signatures from a majority of the federation functionaries could drain the base-layer reserves, rendering the sidechain assets worthless. Fortifying the peg with post-quantum signatures is a critical infrastructure mandate that precedes individual wallet upgrades.
Why Sidechains Serve as Ideal Proving Grounds for Layer-1 Upgrades
Modifying the Bitcoin base layer requires overwhelming social consensus and years of meticulous code review. Sidechains operate with distinct governance models and faster deployment cycles, acting as secure testing environments. The Liquid network's integration of SHRINCS validates the efficiency, fee economics, and operational friction of post-quantum cryptography under real transaction loads. Success in this environment provides the empirical data required to draft a future Bitcoin Improvement Proposal (BIP), ensuring that any eventual Layer-1 upgrade is grounded in proven engineering rather than theoretical modeling.
Charting the Post-Quantum Blockchain Landscape Through 2030
Hardware Requirements for Processing Advanced Cryptographic Proofs
The transition away from elliptic curve cryptography shifts the resource burden onto network validators. Hash-based signatures require more memory and CPU cycles to verify. As sidechains and eventually base layers mandate post-quantum proofs, node operators will face increased hardware demands to maintain current transaction throughput. Optimizations like the Simplicity language mitigate this by executing verifications efficiently, but the baseline computational floor for participating in decentralized consensus will inevitably rise.
Regulatory Pressure from NIST and Global Cybersecurity Frameworks
The push for quantum resilience is not isolated to cypherpunk enclaves. With NIST finalizing its initial post-quantum encryption standards, global regulators are establishing compliance timelines. Agencies such as the SEC and the European Securities and Markets Authority (ESMA) are expected to mandate that institutional digital asset custodians migrate their cold storage infrastructure to quantum-resistant standards before the end of the decade. Networks that fail to provide compatible cryptographic primitives risk being excluded from institutional adoption pipelines.
Conclusion
The race to quantum-proof blockchain networks has shifted from a theoretical exercise to an active engineering mandate. Monitoring how early implementations perform under real-world transaction loads will dictate the timeline for broader Layer-1 adoption.
FAQ
What is SHRINCS and how does it differ from traditional blockchain cryptography? SHRINCS is a post-quantum cryptographic signature scheme designed to resist attacks from quantum computers. Unlike ECDSA, which relies on the difficulty of the discrete logarithm problem, SHRINCS utilizes hash-based cryptography, making it fundamentally immune to Shor's algorithm.
Why are sidechains upgrading to post-quantum standards before the main Bitcoin network? Sidechains operate with different consensus mechanisms and governance models, allowing for faster deployment of experimental upgrades. They act as secure testing environments to validate the efficiency and security of new cryptographic standards without risking the base layer's massive market capitalization.
Sources
Loading comments...
Related
View all →
Enterprise Stablecoin Inflection: Why Corporate Finance is Nearing its 'ChatGPT Moment'




